The Imperative of GovTech Vendor Compliance in a Digital Age
In an increasingly digitized public sector landscape, the significance of GovTech vendor compliance rollouts cannot be overstated. Government agencies, at all levels, are rapidly adopting advanced technologies to enhance efficiency, improve service delivery, and foster greater citizen engagement. However, this digital transformation brings with it a complex web of regulatory requirements, legal obligations, and ethical considerations that demand meticulous attention from GovTech vendors. Non-compliance is not merely a legal headache; it poses substantial risks to public trust, can lead to severe financial penalties, and, most critically, can exclude segments of the population from essential services, undermining the very premise of inclusive digital government.
Today's GovTech vendors are not just selling software or hardware; they are becoming integral partners in the fabric of governance. Their solutions often manage sensitive citizen data, facilitate critical public services, and underpin democratic processes. Therefore, the onus of ensuring that these foundational technologies adhere to stringent standards—from accessibility for all citizens to robust data security and privacy—falls squarely on the shoulders of these providers. A strategic, proactive approach to compliance is no longer a 'nice-to-have' but a fundamental pillar of successful and responsible GovTech partnership.
Navigating the Labyrinth of Regulatory Frameworks
The landscape of GovTech compliance is multifaceted, encompassing a spectrum of legal, ethical, and technical standards. Understanding and meticulously addressing each of these frameworks is paramount for vendors operating in the public sector.
Web Accessibility: ADA Title II, Section 508, and WCAG
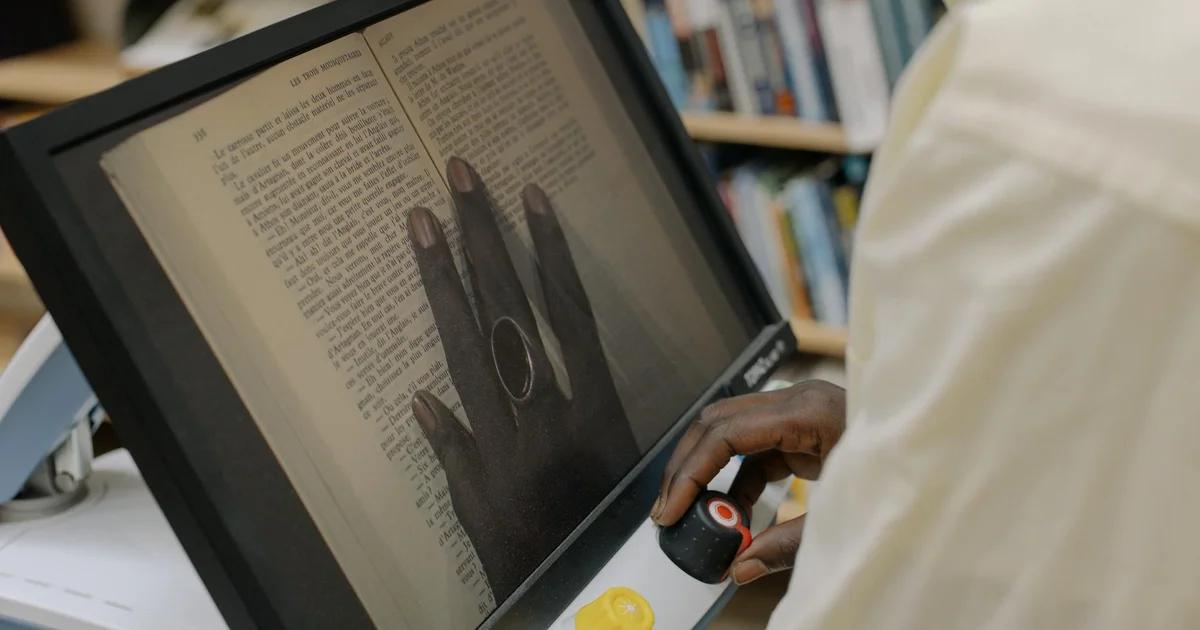
Perhaps one of the most visible and impactful areas of GovTech compliance revolves around web accessibility. Ensuring that digital government services are usable by individuals with disabilities is not just a moral imperative but a legal one, particularly in the United States. The Americans with Disabilities Act (ADA) Title II mandates that state and local government services, programs, and activities be accessible to people with disabilities, extending to their websites and digital platforms. This means that a government agency's new online permit application system, for instance, must be designed to be navigable by someone using a screen reader or keyboard-only navigation.
Complementing the ADA, Section 508 of the Rehabilitation Act specifically requires federal agencies to make their electronic and information technology (EIT) accessible to people with disabilities. While primarily focused on federal procurement, its influence extends to state and local governments through best practices and often, by contract. Many state and local entities adopt Section 508 standards for their own procurements to ensure consistency and a high level of accessibility.
The technical backbone for meeting these legal mandates often comes from the Web Content Accessibility Guidelines (WCAG), developed by the World Wide Web Consortium (W3C). WCAG provides detailed, testable criteria for making web content accessible. GovTech vendors are typically expected to aim for WCAG 2.1 AA conformance, which covers a broad range of accessibility issues related to:
- Perceivable: Information and user interface components must be presentable to users in ways they can perceive.
- Operable: User interface components and navigation must be operable.
- Understandable: Information and the operation of user interface must be understandable.
- Robust: Content must be robust enough that it can be interpreted reliably by a wide variety of user agents, including assistive technologies.
Failing to meet these accessibility standards can lead to costly lawsuits, remediation efforts, and significant reputational damage. More importantly, it can alienate citizens who rely on digital services but are unable to access them due to preventable barriers.
Data Security and Privacy: NIST, GDPR, and State-Specific Regulations
Beyond accessibility, the security and privacy of citizen data are non-negotiable in the GovTech space. Government entities collect and store vast amounts of sensitive information, from social security numbers and health records to financial details and personal communications. Any compromise of this data can have catastrophic consequences.
- NIST (National Institute of Standards and Technology) Frameworks: Many government agencies rely on NIST Special Publications, particularly the NIST Cybersecurity Framework (CSF) and NIST SP 800-53 (Security and Privacy Controls for Federal Information Systems and Organizations), as benchmarks for their cybersecurity postures. GovTech vendors must demonstrate their solutions' ability to integrate with or meet these stringent security controls. This includes secure coding practices, regular vulnerability assessments, penetration testing, and robust incident response plans.
- GDPR (General Data Protection Regulation): While a European Union regulation, GDPR's extraterritorial reach means that any GovTech vendor processing data of EU citizens, regardless of where the processing occurs, must comply. Its principles of data minimization, purpose limitation, storage limitation, accuracy, integrity and confidentiality, and accountability have also influenced data privacy laws globally, including within the US.
- State-Specific Privacy Laws: A growing number of US states are enacting their own comprehensive privacy laws, such as the California Consumer Privacy Act (CCPA) and its successor CPRA, the Virginia Consumer Data Protection Act (VCDPA), and the Colorado Privacy Act (CPA). These laws introduce consumer rights regarding personal data, impose obligations on businesses concerning data collection, use, and sharing, and often require specific contractual clauses for third-party vendors. GovTech vendors must be agile enough to understand and adapt to this evolving patchwork of state-level privacy legislation, ensuring their services can be configured to meet diverse requirements.
GovTech vendors must integrate these security and privacy considerations into every stage of their product lifecycle, from initial design and development to deployment and ongoing maintenance. This requires a 'security by design' and 'privacy by design' philosophy, where safeguards are built in rather than bolted on as an afterthought.
Strategic Planning for GovTech Compliance Rollouts
Successful compliance rollouts don't happen by accident; they are the result of meticulous planning, cross-functional collaboration, and a clear understanding of objectives. For GovTech vendors, this strategic planning phase is critical for minimizing risks and maximizing the chances of a smooth, effective deployment.
Initial Assessment and Gap Analysis
The first step in any compliance rollout is a comprehensive assessment of the current state of a product or service against the required compliance standards. This involves:
- Identifying Applicable Regulations: Clearly defining which specific laws, standards, and guidelines (e.g., ADA Title II, Section 508, WCAG 2.1 AA, NIST, relevant state privacy laws) apply to the GovTech solution and the government client's specific context.
- Baseline Audit: Conducting a thorough audit of existing systems, software, and processes to identify current compliance levels. For accessibility, this might involve automated and manual testing of user interfaces, content, and user flows. For security, it would include vulnerability scans and reviews of data handling practices.
- Gap Analysis: Documenting the discrepancies between the current state and the desired compliant state. This gap analysis forms the basis for the remediation plan, prioritizing areas of highest risk or non-compliance.
Resource Allocation and Team Formation
Compliance is a team sport. Successful GovTech compliance rollouts require a dedicated, cross-functional team with diverse expertise. This team typically includes:
- Legal Counsel: To interpret regulations, draft compliant contracts, and advise on risk.
- Product Development/Engineering: To implement technical changes, adopt accessibility features, and embed security protocols.
- Quality Assurance (QA): To conduct rigorous testing for compliance, particularly accessibility and security testing.
- Project Management: To coordinate efforts, manage timelines, and ensure efficient resource utilization.
- Security & Privacy Officers: To oversee data protection strategies and incident response.
- Accessibility Specialists: To provide expert guidance on WCAG and assistive technologies.
Adequate budget and resources must be allocated for training, tools, third-party audits, and potential re-engineering efforts. Underestimating the resource commitment is a common pitfall.
Developing a Phased Implementation Roadmap
Rather than attempting a 'big bang' approach, GovTech vendors should develop a phased implementation roadmap. This allows for incremental progress, continuous testing, and adaptive adjustments. Key elements of this roadmap include:
- Prioritization: Addressing the most critical compliance gaps first, especially those posing significant legal or functional risks.
- Milestones and Timelines: Setting clear, achievable milestones for each phase, with realistic timelines.
- Stakeholder Communication: Maintaining open and transparent communication with government clients, internal teams, and relevant regulatory bodies (where appropriate) throughout the rollout.
- Pilot Programs: Before a full-scale rollout, consider pilot programs with a subset of users or a limited functionality to gather feedback and refine the compliance approach.
Implementation Best Practices for GovTech Vendors
Once the strategic planning is complete, the focus shifts to effective implementation. This phase is where theoretical compliance strategies are translated into tangible, compliant products and services.
Accessibility by Design and Development
The most effective way to achieve accessibility compliance is to embed it into the very core of the product development lifecycle. This means:
- Early Integration: Involving accessibility experts from the initial design and UX phases, rather than attempting to 'fix' accessibility issues later. This is significantly more cost-effective and leads to superior user experiences.
- Training Developers: Ensuring that development teams are well-versed in WCAG principles, semantic HTML, ARIA attributes, and keyboard navigation best practices.
- Automated and Manual Testing: Using a combination of automated accessibility checkers (for quick scans) and thorough manual testing with assistive technologies (like screen readers) to identify and rectify issues.
- User Testing with Disabilities: Engaging users with diverse disabilities in the testing process to gain invaluable real-world feedback on usability and accessibility.
Robust Security Protocols and Data Governance
Implementing strong security measures and data governance practices is non-negotiable. This involves:
- Secure Software Development Lifecycle (SSDLC): Integrating security considerations into every phase, from requirements gathering to deployment and maintenance. This includes threat modeling, secure coding standards, and security testing.
- Encryption: Encrypting data both in transit and at rest to protect against unauthorized access.
- Access Controls: Implementing strict role-based access controls (RBAC) to ensure that only authorized personnel can access sensitive data.
- Regular Security Audits and Penetration Testing: Proactively identifying vulnerabilities before malicious actors can exploit them. Third-party independent audits lend credibility.
- Data Minimization: Collecting only the data necessary for the service's purpose, reducing the risk exposure.
- Incident Response Plan: Having a well-defined and regularly tested plan for responding to data breaches or security incidents, including communication protocols with affected government agencies and citizens.
Contractual Safeguards and Vendor Due Diligence
GovTech vendors must proactively address compliance in their contracts with government clients and sub-vendors. This includes:
- Clear Compliance Clauses: Specifying which compliance standards the solution adheres to (e.g., WCAG 2.1 AA, NIST 800-53), and detailing the vendor's responsibilities for maintaining that compliance.
- Indemnification: Including clauses that protect the government agency in case of vendor non-compliance.
- Audit Rights: Granting the government client the right to audit the vendor's compliance processes and systems.
- Data Processing Agreements (DPAs): For data privacy, robust DPAs are essential, outlining data protection responsibilities, sub-processor agreements, and breach notification procedures.
- Sub-Vendor Management: Extending compliance requirements to any third-party sub-vendors or partners used by the GovTech provider, ensuring their compliance posture aligns with the primary vendor's commitments.
Cultivating a Culture of Continuous Compliance
Compliance is not a one-time project; it's an ongoing commitment. The regulatory landscape is constantly evolving, technology advances rapidly, and citizen expectations continue to rise. GovTech vendors must embed a culture of continuous compliance into their organizational DNA.
Ongoing Training and Awareness Programs
Regular training is essential for all employees, particularly those involved in product development, design, testing, and customer support. This includes:
- Accessibility Training: Keeping developers, designers, and QA up-to-date on the latest WCAG guidelines and assistive technologies.
- Security Awareness: Educating all staff on phishing, social engineering, data handling best practices, and the importance of strong passwords.
- Privacy Training: Ensuring employees understand data privacy principles and the specific requirements of applicable regulations.
- Role-Specific Training: Tailoring training to the specific responsibilities of different teams.
These programs should not be annual checkboxes but ongoing, engaging initiatives that foster a genuine understanding and commitment to compliance principles.
Regular Audits, Monitoring, and Feedback Loops
Proactive monitoring and regular audits are critical for detecting issues before they escalate. This involves:
- Automated Monitoring Tools: Deploying tools that continuously scan websites and applications for accessibility and security vulnerabilities.
- Periodic Manual Audits: Engaging independent third-party auditors to conduct comprehensive reviews, providing an unbiased assessment of compliance status.
- User Feedback Mechanisms: Establishing clear channels for government clients and end-users (including individuals with disabilities) to report accessibility or security concerns. Promptly addressing this feedback is crucial.
- Regulatory Watch: Designating a team or individual responsible for tracking changes in relevant laws, regulations, and industry standards, and ensuring the organization adapts accordingly.
- Performance Metrics: Defining key performance indicators (KPIs) for compliance (e.g., percentage of WCAG 2.1 AA compliant pages, number of security vulnerabilities remediated within a timeframe) and regularly reporting on them.
The Role of Agile Compliance and DevSecOps
Modern software development methodologies, like Agile and DevSecOps, offer powerful frameworks for integrating compliance into continuous delivery pipelines.
- Agile Compliance: Breaking down compliance requirements into smaller, manageable tasks that can be addressed in sprints. This allows for iterative development, testing, and remediation, making compliance an integral part of each release rather than a post-development hurdle.
- DevSecOps: Blending development, security, and operations. This approach automates security testing and compliance checks throughout the CI/CD pipeline, ensuring that security and accessibility are continuously validated from code commit to deployment. It shifts security 'left,' integrating it earlier in the development process, reducing the cost and effort of fixing issues later.
The Business Value Beyond Compliance
While avoiding legal penalties and reputational damage are strong motivators, GovTech vendor compliance offers substantial proactive business advantages that extend beyond mere obligation.
Enhanced Market Competitiveness and Trust
In a competitive GovTech market, vendors with a proven track record of robust compliance stand out. Government agencies are increasingly prioritizing compliant solutions, especially in areas like accessibility and data security. Demonstrating a proactive commitment to these standards builds immense trust, positioning a vendor as a reliable and responsible partner. This trust is a significant competitive differentiator and can lead to stronger, longer-term contracts.
Improved User Experience and Wider Reach
Accessibility features, far from being just for users with disabilities, often improve the overall user experience for everyone. Clear navigation, well-structured content, keyboard operability, and intuitive interfaces benefit all users, regardless of their abilities. By adhering to WCAG standards, GovTech solutions become more usable, efficient, and inclusive, reaching a broader segment of the population and enhancing citizen satisfaction with government services.
Reduced Costs and Technical Debt
Integrating compliance early in the development lifecycle (accessibility by design, security by design) is significantly more cost-effective than remediating issues after launch. Retrofitting accessibility features or patching security vulnerabilities in deployed systems can be incredibly expensive, time-consuming, and technically challenging. A 'shift left' approach to compliance reduces technical debt and minimizes the need for costly rework.
Operational Efficiency and Risk Mitigation
A well-defined compliance framework leads to clearer processes, standardized practices, and improved internal controls. This operational efficiency reduces errors, streamlines workflows, and ensures a more predictable and stable service delivery. Furthermore, a robust compliance program acts as a powerful risk mitigation strategy, protecting both the vendor and the government client from legal challenges, data breaches, and service disruptions.
Future Trends in GovTech Compliance
The GovTech compliance landscape is dynamic, shaped by technological advancements, evolving societal expectations, and emerging threats. Vendors must keep an eye on future trends to remain agile and competitive.
Proactive Regulatory Anticipation
Governments are increasingly looking to proactively address future challenges, especially concerning artificial intelligence (AI) and emerging technologies. GovTech vendors should anticipate regulations related to:
- Ethical AI: Guidelines around transparency, bias, accountability, and explainability in AI systems used in the public sector. For example, ensuring AI algorithms used in social services or judicial support are fair and non-discriminatory.
- IoT Security: As smart city initiatives grow, securing Internet of Things (IoT) devices and their data will become a major compliance area.
- Digital Identity: Standards and regulations for secure, verifiable, and inclusive digital identity solutions.
Global Harmonization and Interoperability
While national and state-specific regulations currently dominate, there's a growing movement towards global harmonization of standards, particularly in areas like data privacy and cybersecurity. GovTech vendors operating across different jurisdictions may see increased pressure to align with internationally recognized best practices, facilitating greater interoperability and reducing the burden of managing disparate compliance regimes.
The Rise of AI in Compliance Management
Artificial intelligence and machine learning (AI/ML) are poised to revolutionize compliance management itself. AI-powered tools can:
- Automate Compliance Checks: Faster and more accurate identification of accessibility issues, security vulnerabilities, and data privacy violations within codebases and deployed systems.
- Regulatory Intelligence: Analyze vast amounts of regulatory text to identify changes, interpret implications, and recommend necessary adjustments to compliance programs.
- Predictive Compliance: Use historical data to anticipate potential compliance risks and suggest preventative measures before issues arise.
However, the use of AI in compliance also raises questions about the AI's own biases and transparency, which themselves become compliance considerations.
Enhanced Citizen Scrutiny and Demand for Transparency
As citizens become more digitally literate and aware of their rights, the demand for transparency and accountability from both governments and their technology vendors will intensify. This will translate into greater public scrutiny of compliance records, data handling practices, and the ethical implications of GovTech solutions. Vendors who proactively engage with citizen feedback and transparently communicate their compliance efforts will build stronger relationships.
Conclusion: Compliance as a Foundation for GovTech Excellence
In essence, GovTech vendor compliance rollouts are far more than a legal obligation; they are the bedrock upon which trust, efficiency, and equitable public service delivery are built. From ensuring digital services are accessible to every citizen, regardless of ability, to safeguarding sensitive personal data against sophisticated cyber threats, the demands on GovTech providers are stringent and ever-increasing. By embracing a proactive, 'by design' approach to compliance—integrating accessibility, security, and privacy throughout the entire product lifecycle—vendors can mitigate risks, differentiate themselves in a competitive market, and ultimately contribute to a more inclusive and resilient digital government ecosystem. The future of GovTech belongs to those who view compliance not as a hurdle, but as an indispensable investment in excellence and public good. This strategic foresight transforms compliance from a mere requirement into a powerful catalyst for innovation and sustainable partnership within the public sector.